
Ransom X Ransomeware attacks Texas Department of Transportation TxDOT
RansomX is a new ransomware used actively in human-operated and targeted attacks against government agencies and enterprises.In May 2020 two Texas state agencies were attacked, the Texas Court and the Texas Department of Transport(TxDOT) were hit by a ransomware attack.
At the time of the attacks , it was not known what ransomware targeted the agencies
RANSOM X
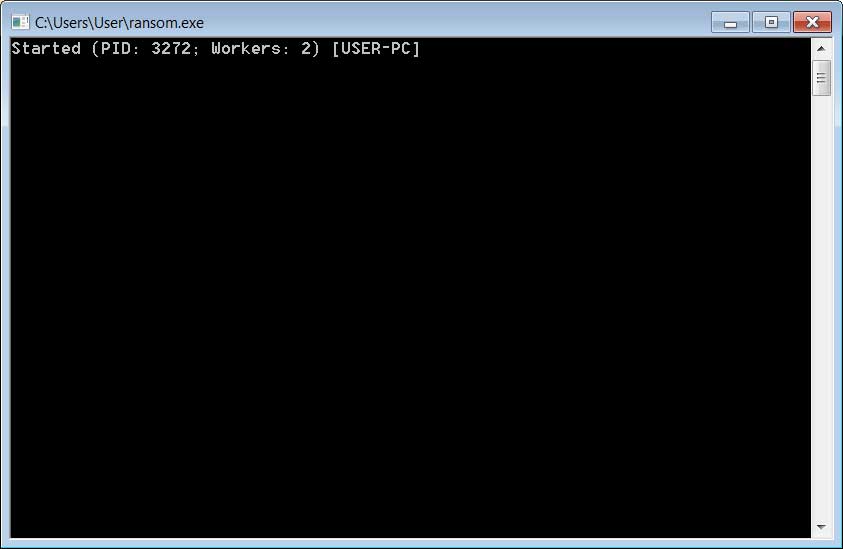
This is a human-operated ransomeware, rather than one distributed via phishing or malware, when executed the ransomware will open a console that displays information to the attacker while it is running.
This ransware bypass various windows system folders and any files that match the follow extensions:
.ani, .cab, .cpl, .cur, .diagcab, .diagpkg, .dll, .drv, .hlp, .icl, .icns, .ico, .iso, .ics, .lnk, .idx, .mod, .mpa, .msc, .msp, .msstyles, .msu, .nomedia, .ocx, .prf, .rtp, .scr, .shs, .spl, .sys, .theme, .themepack, .exe, .bat, .cmd, .url, .muiother computers on the network without fear their tools will become encrypt.
Ransom X also perform a series of commands throughout the encryption process that:
- Delete NTFS journals
- Disable Windows Recovery environment
- Delete Windows backup catalogs
- Deletes Windows backup catalogs
- Clears Windows event logs
- Wipe free space from the Local drives.
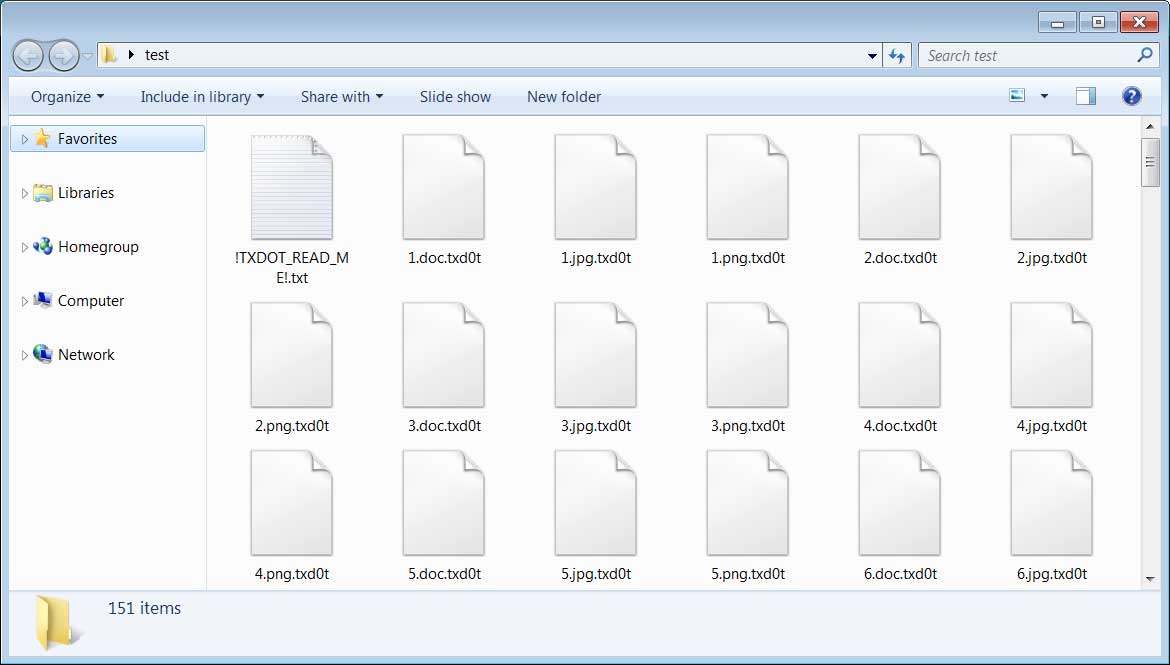
Below is an example of the Texas Department of Transport attack was .txdot.
Comments
Post a Comment